We produce and source LED lights for events in China, You find the right place to get all the LED lights for events!
Manufacturer of LED lights for events
Manufacturer of LED lighting for events
Your one-stop solution for events lighting!
JEJA International Corporation Limited is your ideal Manufacturer of LED lighting for events and a one-stop purchasing agent in China! You can buy the most cost-effective products produced by us own. Or we help you buy the finest products produced by other Chinese suppliers as well. We offer you the best products from China, our best service, and purchasing solutions. Come to us if you have an idea and want to turn the idea into products; Come to us if you need someone to help you inspect a factory or products; Come to us if you want to find out what the suitable lights for your market are...
How JEJA can help you with your business?
What LED lighting for events we are offering to you
Our own LED lighting for events products
Designed and produced by ourselves
You can find our fine-designed LED lighting for events on the product page. We have been designing and producing remote-controlled led lights according to the demand of the market and customers for over 10 years. There are about 10 products very popular in the market and copied by competitors. We are good at designing IR remote-controlled LED lights, RF remote-controlled LED lights, and Bluetooth-controlled led lights. These lights are widely used for wedding decoration, events design, home decoration, etc...
OEM & ODM LED lighting for events
Turn your ideas into products and boom your business!
You can turn our LED lighting for events into your own with your LOGO or package. And we can turn your ideas of light into a real product. We helped draw 3D pictures, make testing prototypes, built molds, make PCBs, and produce lights for our customers. All these were at a very reasonable cost and fast delivery! We have an R&D team with 3 engineers and many co-engineers who are ready to help you any time. The co-engineers are in the fields of mold designing, material, electronics, telecommunication, and product structure. Making new LED lights for our customers brings us great joy!
Sourcing LED lighting for events in China
Everything you need from China can be found by us.
No need to come to China so often to look for factories or products! No need to worry about payment safety!
Once you order from us, you'll find out that we are trustworthy!
Once you trust us, we'll be your best Chinese partner!
Just tell me the product you need, we will get the best solution for you. We have been helping some customers purchase wedding lights, wall lights, orb lights, candle lights, uplighting, hexagon lights, table lamps, stage lights and balloon lights, etc....
We can help you find the best LED lights for your wholesale business, retail, e-shop, rental, or event design business.

Factory and product inspection
You will have eyes and ears afar!
No need to come to China to inspect factories of LED lighting for events products!
No need to worry about the quality of your ordered products!
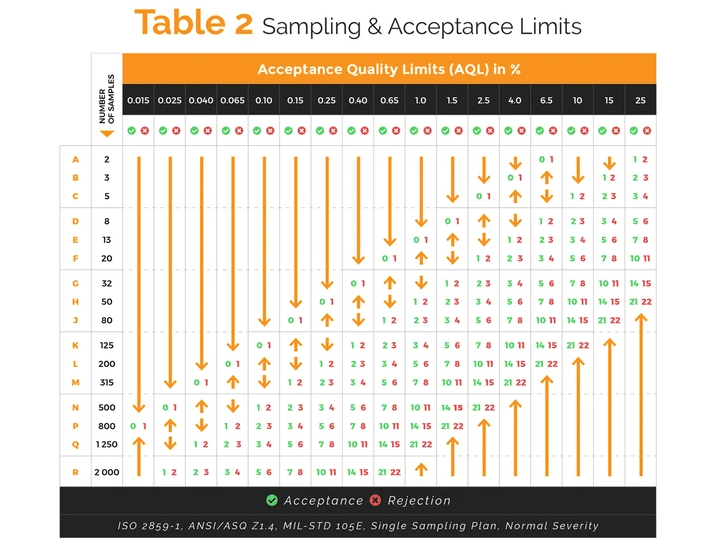
Let us know your AQL, we will be your quality guard.
With more than 10 years experience in quality control, we are your reliable inspectors. We helped tens of thousands of customers inspect their new suppliers and products. The total satisfaction ratio is over 93%. We know the problems with LED lighting products, so we can easily get to the point. There is a long list of the products we inspected, including LED light base, submersible led candles, remote controlled lightbase, rechargeable light base for centerpieces, ball lights, remote controlled orb lights, Forster egg lights, Christmas decorating lights, motion sensor cabinet lights, solar lights, and strip lights, etc...
Helping arrange payment and shipping
We are your financial and logistics department in China.
We can pay RMB to your other suppliers in China after you send us USD. We can even help you make payment with our own money under certain conditions. No need to worry about being cheated.
We offer the service of collecting small orders from various suppliers and ship together, find the best shipping way at a certain time. Fast, cheap are our goals of shipping!
Get in touch
Do you want to add some light to your life?
We have the perfect solution for you. Our square lights are a great way to add some color and excitement to any room in your home or office. You can even use them outside on patios or decks! They’re easy-to-use, too – just plug them into an outlet and control them with our RF remote control!
With 9 fixed colors and over 40 dynamic modes, there’s always something new going on with these lights. And they sync up perfectly with whatever music is playing nearby, so it feels like the party never ends! Plus, they’re made from durable ABS plastic that will last for years of enjoyment. What more could you ask for?
Contact us right now and order a set of square lights today!

New products!
The Quarter canvas lights are ready!
Key features :
1, IR remote + touch to control the canvas
2, 13 fixed colors and 3 dynamic color modes on remote
3, 8 fixed colors and 2 dynamic color modes by touching
4, USB connectors to link the canvas
5, With a stand to put on the table
Please contact us below for more information
Touch sensitive wall light
New version--many colors available
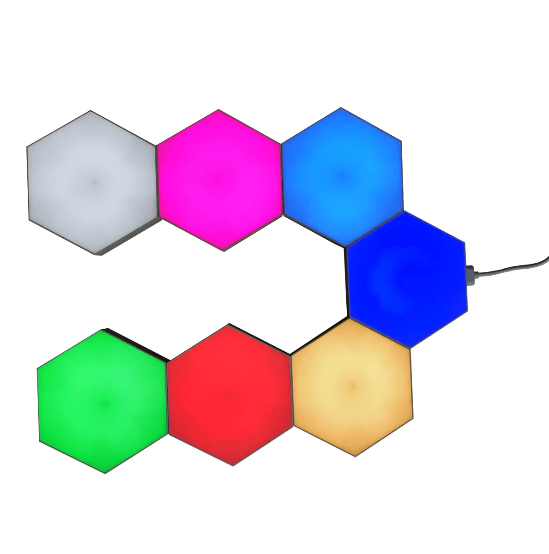
Hexagon lights turn on and off individually with a tap of the hand. This will either give you further lighting customization control, plus some fun tactile times with illumination or make it really irritating to turn your lights on and off, especially if you go full throttle with the hexagon lights.
The hexagonal wall lights consist of flat hexagon modules fitted with LEDs and USB port edges so you can mount them to your wall in any pattern or design you like. The lights attach to walls with adhesive pads.
There are many colors available: white, warm white, red, green, blue, pink, etc...
Programmed hexagon LED light
Special recommendation--over 300 modes
RF remote controlled dynamic hexagonal LED light is easy to be connected one another with USB boards. You can make them in various shapes you like. For instance, a heart, a flower, a line, a big panel, circles, animal shapes or business logos, etc...
It's used to put on walls of KTV, bars, dancing halls, sitting rooms, and shops for music. Also, the light is suitable for event design. For example, a big welcome panel for a wedding, dynamic line on the wall, decoration on tables or decorate the edge of the stage, etc...
There are over 300 dynamic color-changing modes for you to enjoy.
Best selling LED lighting for events
New LED lighting for events
Some knowledge about LED lighting for events
GET TO KNOW THE LIGHTING LINGO
Before you start looking for lighting ideas or reaching out to vendors for quotes, you’ll want to know these key wedding lighting terms so you’ll know what you (and the pros) are talking about:
Uplighting – lights that are placed on the floor and shine up the walls in various colors
Gobo light – a template that light shines through to create a pattern, monogram, or motif on the floor, ceiling, or wall
Texture lighting – the same as a Gobo light but with a preset pattern, such as leaves or a starry night sky
Spotlight – a lamp that projects a narrow beam of light on one particular area or object
Pinspot – a tiny light used to illuminate a small area, such as a centerpiece on a table
String lights – also referred to as twinkle, fairy, bistro, or cafe lights, these strands of lights are the most versatile and cost-effective way to light up any space
Pendants – also known as drop or suspender lights, these are single fixtures that hang from the ceiling
LED light – type of bulb that is cost-effective, long-lasting, and provides more vibrant color than a traditional bulb
Color wash – a general fill of color used throughout an entire room that doesn’t highlight any particular area
WEDDING LIGHTING IDEAS BY STYLE
Romantic – If your style is romantic and classic, you can’t go wrong with tons of candlelight, string lights, and crystal chandeliers. Keep the glow soft and warm to create a cozy ambiance that makes guests feel welcome and relaxed.
Rustic – If your style is more rustic, antique lanterns, paper lanterns, Edison bulb pendant lights, and marquee lights can help you bring a raw, natural feel to your wedding design. Your mood should have an at-home feel, which requires simple lighting with a hint of charm.
Modern – If your style is modern and minimal, hurricane vases with floating candles, spotlights, and color washing can provide drama without too much fuss. You’ll probably want to opt for LED lights because they provide more vibrant colors than traditional bulbs.
Glamorous – If you love a glamorous style, you’ll want to go for more dramatic lighting sources, such as crystal chandeliers, candelabras, lit topiaries, and curtains of lights. Since nothing says glam like a little glitz, make sure to add sparkly details near the lighting sources so they reflect and add a glow to the room.
In addition to your wedding style, you should also think about what elements of your wedding are most important to you. If you invested a large portion of your budget into the flowers, you’ll want to be sure they’re sufficiently lit with pin spots or candles so your guests can see every detail. If you’re more interested in getting everyone on the dance floor, consider disco balls and gobo or texture lights to keep the party vibe up all night long.
TIPS FOR INDOOR AND OUTDOOR WEDDING LIGHTING
Indoor LightingFor an indoor wedding, you’ll need to know what lighting is already in the venue so that you can simply add to it or work around it. Uplighting is great for accentuating architectural features or changing wall colors to match your palette, and color washing can help create different moods in different rooms throughout the venue. This is where a lighting design pro will be your best friend! They can help figure out what existing fixture will work and what to add to get the look you want.
Outdoor LightingFor an outdoor wedding, power sources will likely be your biggest roadblock. If you’re getting married at night, you’ll also want to make sure all pathways to the venue, to the parking lot, and to the bathrooms are lit. For a small backyard wedding, you will likely be good with simple string lights in and between trees and votive candles on every table. But, if you’re having a big outdoor celebration in a courtyard or tent, you’ll want to call in the professionals! They might need to bring in generators for more power and will save you the hassle of trying to hang lights in high places.
A guide to choosing the right lights for your home
Lighting options are available in a variety of budgets, from traditional to contemporary styles. Fixtures crafted in metals, glass, crystals, bamboo, and fiber, come in different sizes and shapes. Floor lamps, wall scones, ceiling lamps, spot and pendant lights, chandeliers, and light strips, can also be used in a home’s décor.
Before selecting the fixtures and deciding on their placement, one needs to have a clear idea about the purpose of the lighting. “The aim should be to minimize the number of fixtures and maximize their effect and functionality,” points out Komal Vasa, a lighting and interior designer from Mumbai.Lighting tips
The main lighting source should be bright. You can use LED lights of relevant wattage, to give a comfortable feeling.
Consider the ceiling height, before hanging a chandelier. It should be mounted at least seven to eight ft above the floor.
On a workstation, place the lamp at a correct angle, to ensure that no shadow falls on the working area.
A side table with a lamp, not only has its own charm but is also useful as a reading light.
Lamps in the bedroom need to be at a convenient distance from the bed, making them easy to operate.
While selecting light fixtures, ensure that it complements the overall theme of the house and furniture design.
Choose fixtures that are easy to maintain – spares and accessories should be easily available in the future, for replacement.
Ensure that the children’s rooms are bright. Avoid floor lamps and glass lamps for safety.
Always have extra plug points for lights (like fairy lights and lamps) that you can use during festivals and special occasions.what's new in our facebook
Brother companies
LED Lights All .com
Brother companies
Hexagoanlight.com
Brother Companies
jejasz.com
Brother Companies
Commdy.com
What are you waiting for?
JEJA International Corporation Limited is ready to offer you our best products and services!

About Us
JEJA International Corporation Limited is your idealest one-stop purchasing agent in China!
Contact
Mr. Ethan Peng
+86 18929390369
info@
Live chat
whatsapp: +8618929390369
Skype: pethan98021
wechat: ethanjeja
JEJA© 2022